As the implementation of artificial intelligence (AI) expands across industries, securing AI-powered cloud infrastructures has become a paramount concern. This comprehensive guide delves into the multifaceted aspects of ensuring your AI-driven cloud systems, equipping you with the tools to mitigate vulnerabilities and foster a secure and trustworthy environment.
- First, we'll explore the unique security considerations posed by AI-powered cloud solutions.{
- Subsequently, we'll delve into best practices for securing your data, models, and {infrastructure|. We'll cover key concepts such as access control, encryption, and threat analysis.
- Additionally, we'll discuss the role of governance in securing AI-powered cloud operations.
Ultimately, this guide will provide you with a holistic understanding of the techniques necessary to defend your AI-powered cloud environment, enabling you to harness the power of AI while minimizing vulnerabilities.
Mitigating AI-Driven Threats in the Cloud Landscape
The dynamic cloud ecosystem presents a unprecedented landscape for innovation, but it also creates fertile ground for novel AI-driven threats. These threats can range from data breaches and fraudulent code execution to synthetic media and {algorithmic bias|. To effectively address these risks, a multi-layered approach is crucial. This involves implementing robust security more info protocols, leveraging AI-powered threat detection systems, fostering a culture of security awareness, and continuously assessing the evolving threat landscape. By adopting a proactive and holistic strategy, organizations can strengthen their defenses against AI-driven threats and ensure the integrity and resilience of their cloud environments.
Securing the Cloud Leveraging AI for Proactive Defense
In today's dynamic digital landscape, cloud computing has become critical for businesses of all sizes. However, this shift to the cloud also presents new threats that require innovative solutions. Artificial intelligence (AI) is emerging as a game-changing tool to bolster cloud security and enable proactive defense against ever-evolving threats.
By leveraging AI-powered analytics, organizations can identify anomalous activities, predict potential vulnerabilities, and automate mitigation efforts. This allows for a more agile and effective security posture, significantly reducing the damage of cyber threats.
AI can be deployed across various aspects of cloud security, including:
* Threat detection and prevention: AI algorithms can analyze network traffic, system logs, and user behavior to identify malicious patterns and prevent attacks in real time.
* Vulnerability assessment and management: AI can automate the process of identifying and assessing vulnerabilities in cloud infrastructure and applications, allowing for prompt remediation.
* Security information and event management (SIEM): AI-powered SIEM systems can analyze security logs from multiple sources to provide actionable insights and accelerate incident response.
Continuous monitoring and threat intelligence: AI can continuously monitor the threat landscape, identify emerging threats, and provide organizations with proactive intelligence to strengthen their defenses.
The Evolving Landscape: AI and Cybersecurity in the Cloud
In today's rapidly evolving digital landscape, where cloud computing has become ubiquitous, the intersection of artificial intelligence (AI) and cybersecurity presents a compelling narrative. This symbiotic relationship empowers organizations to bolster their defenses against an ever-increasing array of threats. AI algorithms, with their ability to analyze vast datasets and recognize anomalies, serve as a crucial asset in safeguarding cloud environments. By utilizing the power of machine learning, security tools can continuously adapt to emerging threats, mitigating risks before they can manifest.
- Furthermore
AI-driven cybersecurity solutions offer a range of benefits, including:
* Enhanced threat detection and response times
* Improved security posture through automation
* Reduced reliance on manual security tasks
As the cloud continues to transform, the synergy between AI and cybersecurity will become even more essential in ensuring the protection of sensitive data and critical infrastructure.
The Evolving Threat of AI-Enabled Attacks on Cloud Infrastructure
The dynamic landscape of cybersecurity is constantly evolving, with attackers relentlessly leveraging new methods to compromise sensitive data and critical systems. Among the most troubling recent developments is the growth of AI-enabled attacks targeting cloud infrastructure. These sophisticated assaults leverage the power of artificial intelligence to circumvent traditional security defenses, posing a grave threat to organizations of all dimensions.
- AI-powered attackers can execute attacks at an unprecedented scale, carrying out a multitude of simultaneous assaults to overwhelm security defenses.
- Furthermore, AI algorithms can process vast amounts of data to discover vulnerabilities and exploit weaknesses in cloud designs.
- Consequently, organizations must adopt robust security measures that can effectively defend against these AI-driven threats.
Creating Trustworthy AI Systems in a Secure Cloud Environment
As the integration of artificial intelligence (AI) grows across various industries, ensuring the trustworthiness and security of these systems becomes paramount. A reliable cloud environment provides a foundation for building verifiable AI, enabling transparency in algorithms and preserving sensitive data.
Key elements in achieving this include implementing comprehensive testing protocols, adhering to industry best practices for data handling, and leveraging advanced security measures to mitigate the risk of vulnerabilities. By fostering a culture of security and cooperation between developers, data scientists, and security experts, organizations can aim to build AI systems that are both capable and ethical.
 Rick Moranis Then & Now!
Rick Moranis Then & Now! Molly Ringwald Then & Now!
Molly Ringwald Then & Now! Destiny’s Child Then & Now!
Destiny’s Child Then & Now! Joshua Jackson Then & Now!
Joshua Jackson Then & Now!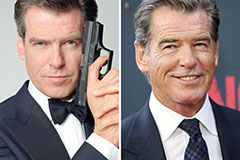 Pierce Brosnan Then & Now!
Pierce Brosnan Then & Now!